Know more!
If you want to know more about the inner life of files, FileAlyzer is the tool you urgently need!
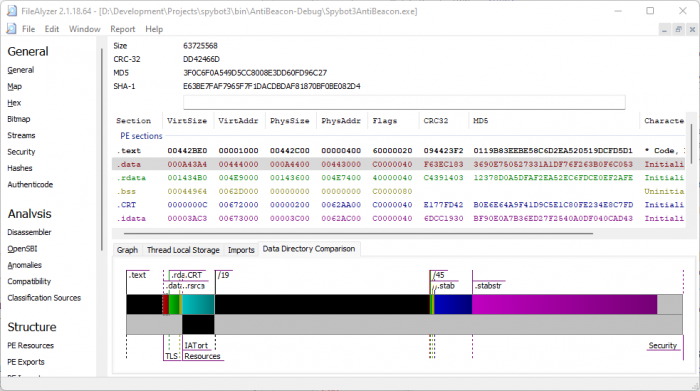
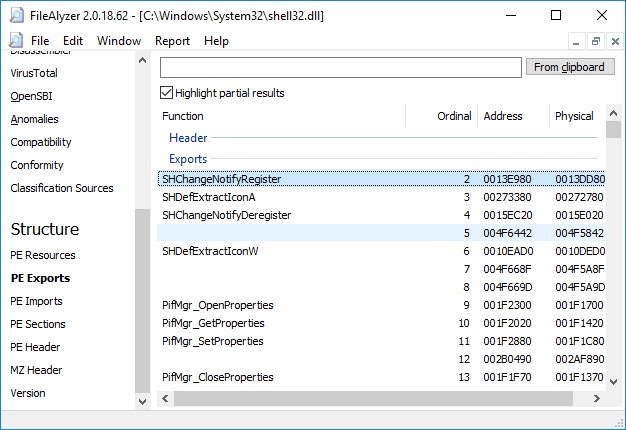
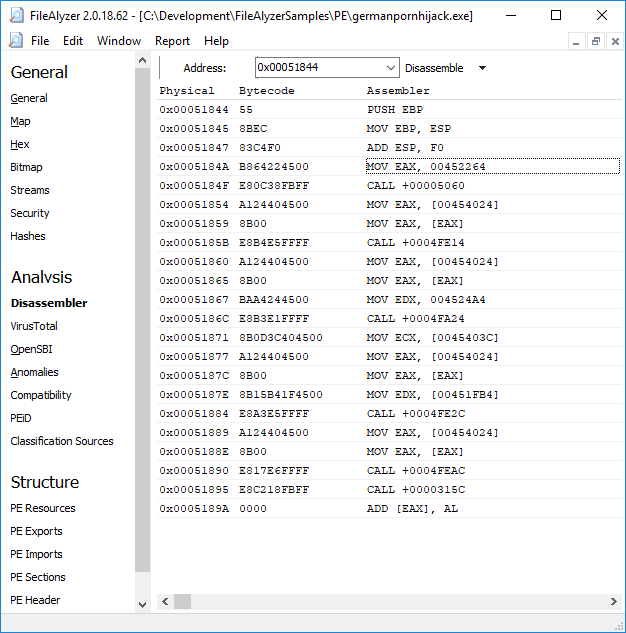
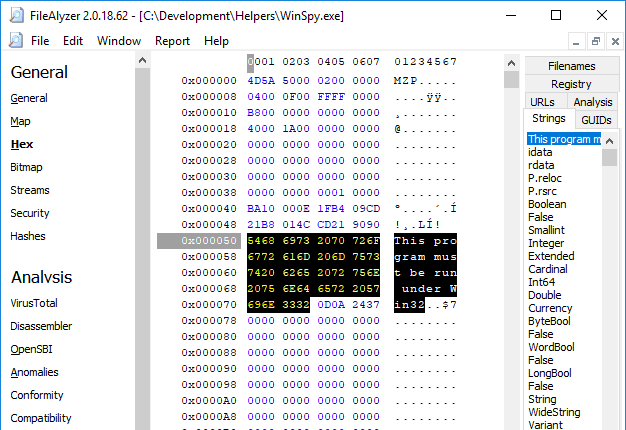
FileAlyzer shows basic file content, a standard hex viewer, and a wide range of customized displays for interpreted complex file structures that help you understand the purpose of a file.
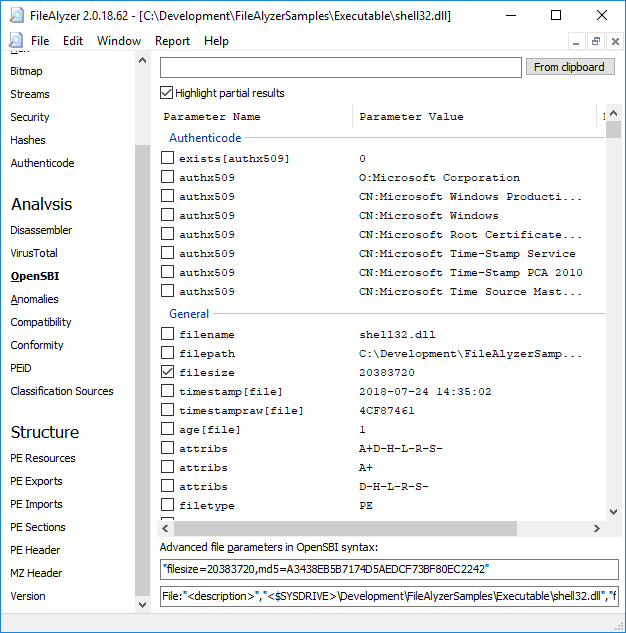
It also supports generation of OpenSBI advanced file parameters – with FileAlyzer you can find the right attributes to write your own optimized malware file signatures!
Features
Anomaliescontinue reading |
External Classification Sourcescontinue reading |
HashesFileAlyzer generates a wide range of standard and rare file checkums and hashes. continue reading |
OpenSBIcontinue reading |
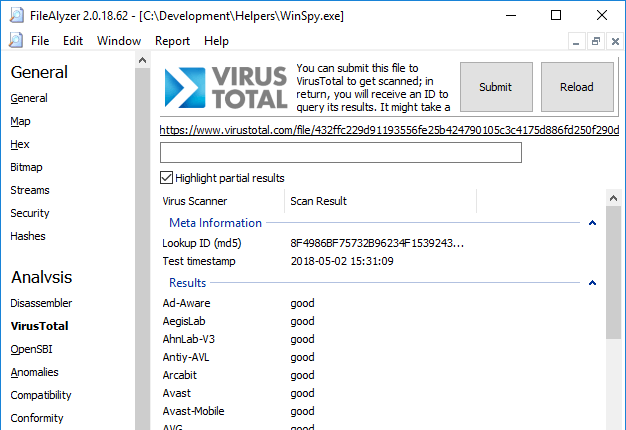
VirusTotal Lookupcontinue reading |
Android appscontinue reading |
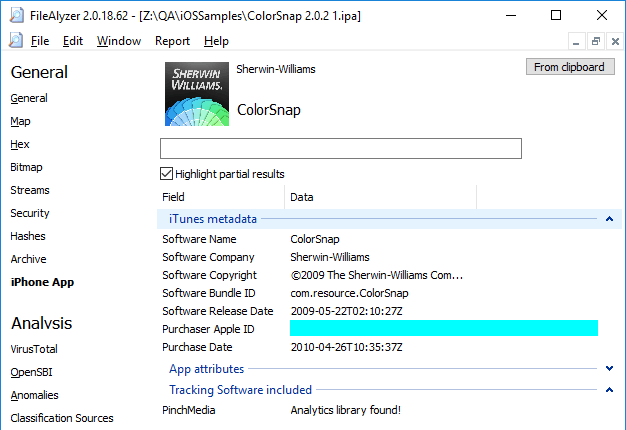
iOS Appscontinue reading |
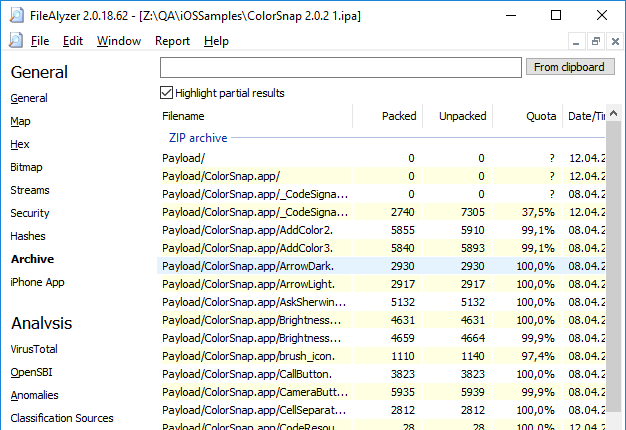
Archivescontinue reading |
Databasescontinue reading |
Delphi Code Mapcontinue reading |
EXIFcontinue reading |
HTMLcontinue reading |
Imagescontinue reading |
InCtrl5 Logscontinue reading |
INI filescontinue reading |
Media Tagscontinue reading |
Textcontinue reading |
ELF Headercontinue reading |
ELF Sectionscontinue reading |
Alternate Data StreamsThis view makes hidden alternate data streams and their content visible. continue reading |
Authenticode Signaturescontinue reading |
MZ Headercontinue reading |
OS CompatibilityCompatibility with various Windows versions, and identification of technology used by malware. continue reading |
PE Disassemblercontinue reading |
PE Exportscontinue reading |
PE Headercontinue reading |
PE Importscontinue reading |
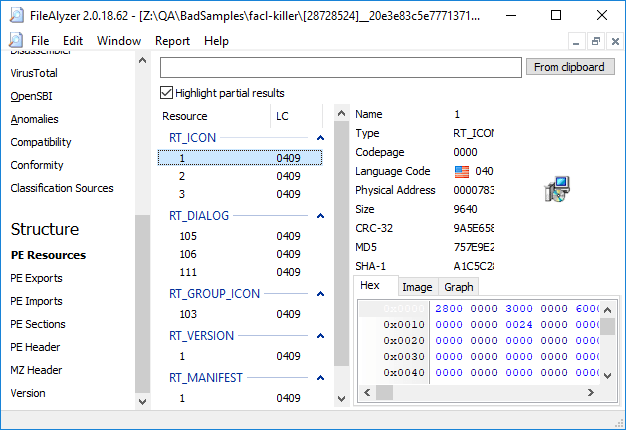
PE Resourcescontinue reading |
PE Sectionscontinue reading |
PEiD (Packers, cryptors and compilers)continue reading |
Prefetch filescontinue reading |
Scheduled Taskscontinue reading |
| Spybot File Scan |
UPX Detailscontinue reading |